How It Works
If you already have external discovery, this is the layer that verifies, prioritizes, and packages findings for review.
How Fusionstek Works
From raw external findings to verified, report-ready outcomes.
Fusionstek keeps the external inventory current, but the value is what happens next: finding validation, drift classification, and evidence exports that hold up in audit and insurer review.
Teams use this to reduce BAS-style retesting cycles for internet-facing issues and avoid building custom CI/SOAR pipelines just to categorize scanner noise.
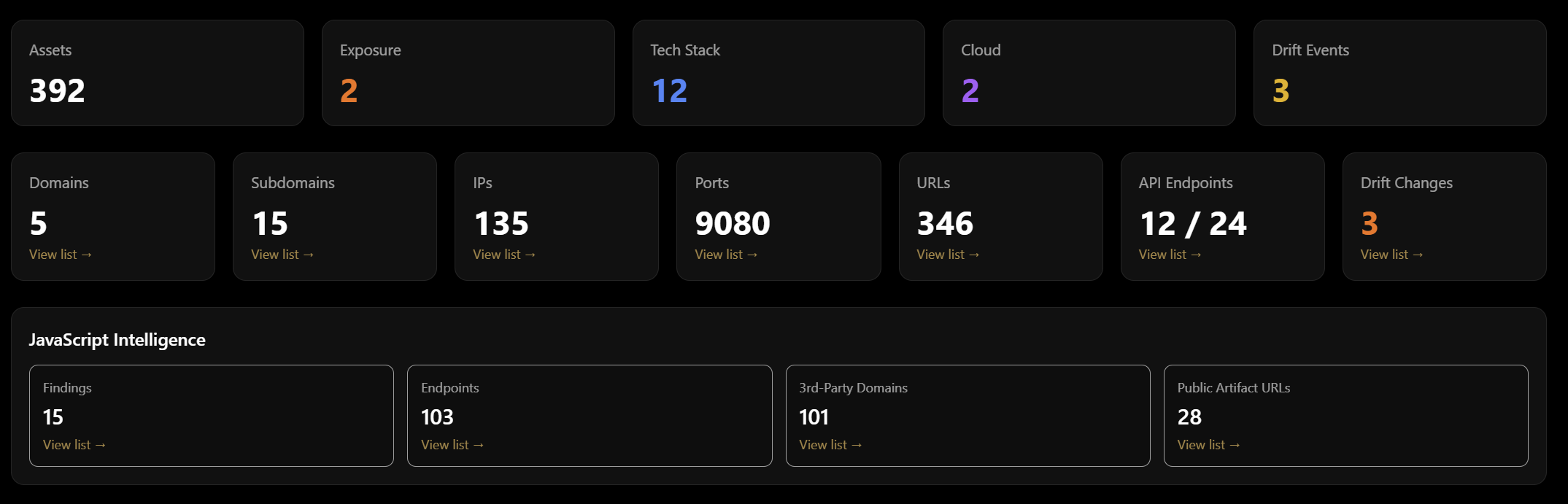
Discovery
Identify every internet-facing asset: domains, subdomains, IPs, ports, URLs, APIs, and cloud. One verified map of what attackers can see, built from real external attack surface discovery.
Monitoring
Continuous tracking of your attack surface. Drift detection shows what’s new, changed, or gone—so you see risks as they appear.
Assessment & Validation
Scan for vulnerabilities, then validate before escalation: reachability, context, and control behaviour are checked. Only evidence-backed, exploitable findings are promoted to reports and tickets—no raw scanner dump.
Intelligence
Breach and credential exposure visibility (e.g. domain-level breach data), threat context, and signals that matter for prioritisation.
Reporting
Dashboards, management summaries, and detailed reports. Export what you need for ops, leadership, and audits.
Regulator Assurance
Verifiable activity record, due-care timeline, and evidence-grade deliverables so compliance and insurers can trust the story.
How the workflow runs
Four steps from scope to verified evidence.
Define Scope
You provide domains and approved scope. Policies enforce what can be tested and how.
Discover & Map
We enumerate internet-facing assets and maintain a verified external map.
Monitor, Validate & Classify
Drift and assessment run on your scope. Findings are validated and classified before escalation so reports include only what we can prove.
Deliver Evidence
You get audit-ready reports, drift timelines, and evidence packs tied to each finding.
What You Get
Outcomes that remove proof and pipeline overhead.
Verified Asset Inventory
A continuously updated map of internet-facing assets with reachability evidence.
Evidence-Grade Findings
Findings are validated before escalation. Reports include reproducible evidence, attack-path context, and timelines.
Assurance Over Time
Daily refresh and drift detection show what changed since the last approved baseline.
Audit-Ready Reports
Structured reporting with clear provenance, timelines, and compliance-ready evidence.
Policy-Driven Guardrails
Compliance-safe execution with explicit scope, consent, and prohibited-action controls.
Disclosure Readiness
Clear timelines of what was known, when, and what was verified.
Frequently Asked Questions
Common questions about implementation and fit.
Ready to see the workflow on your scope?
Book a demo and we will walk through validation, drift, and evidence exports on a real domain set.
Book a Demo