Validate reachable external risk — not just scanner output.
We map scoped external surface, separate confirmed findings from risk signals, show what evidence supports action, and help teams reduce attacker opportunity across external assets — and AI Shadow Assurance applies the same validation standard to external AI and third-party exposure correlation.
Built for security-led teams in
- Enterprise
- Financial Services
- Public SaaS
- Regulated Sectors
- Mar 2026Workspace Callouts: Assurance Health, Exposure, and Drift at a Glance
- Feb 2026Assurance Workspace: Drift Summary and Validation Freshness Signals
- Jan 2026Evidence-First Reporting for Regulator and Insurer Conversations
01 · Risk
Unverified Exposure Doesn’t Survive Scrutiny
After incidents, teams must show what they saw, when they saw it, and what they did. We keep that record current.
External Exposure Blind Spots
Unknown internet-facing assets create attacker opportunity you are not tracking.
Verification Gaps
Raw scanner output without evidence makes auditor and insurer review harder.
Assurance Over Time
One-time scans miss change. Teams need evidence that helps reduce exploitable exposure windows.
Discovery is not the hard part. Validation is. Reports separate validated findings from risk signals so teams can act without mixing confirmed issues with candidates that need review.
02 · Approach
Not Another ASM Inventory Bill
If you already pay for external discovery, the gap is validation, baseline drift, and review-ready exports—not more host lists.
Most ASM stops at “here is what we found.” Fusionstek validates reachable external risk, separates confirmed findings from risk signals, and preserves evidence for review.
Attacker’s View: Logic, Mindset & Timing
Prioritize attacker-relevant exposure paths and show what evidence supports action.
Verification-First Findings
Validate reachable external risk before promotion, then separate validated findings from risk signals.
Review-Ready Reporting
Reports include timestamps, verification method, and status history for review.
Assurance Over Time
Compare current external evidence against a baseline to see what appeared, disappeared, changed, or regressed.
03 · Workspace
One View of Exposure, Drift, and Validation
See open exposure, recent change, and validation status in one view.
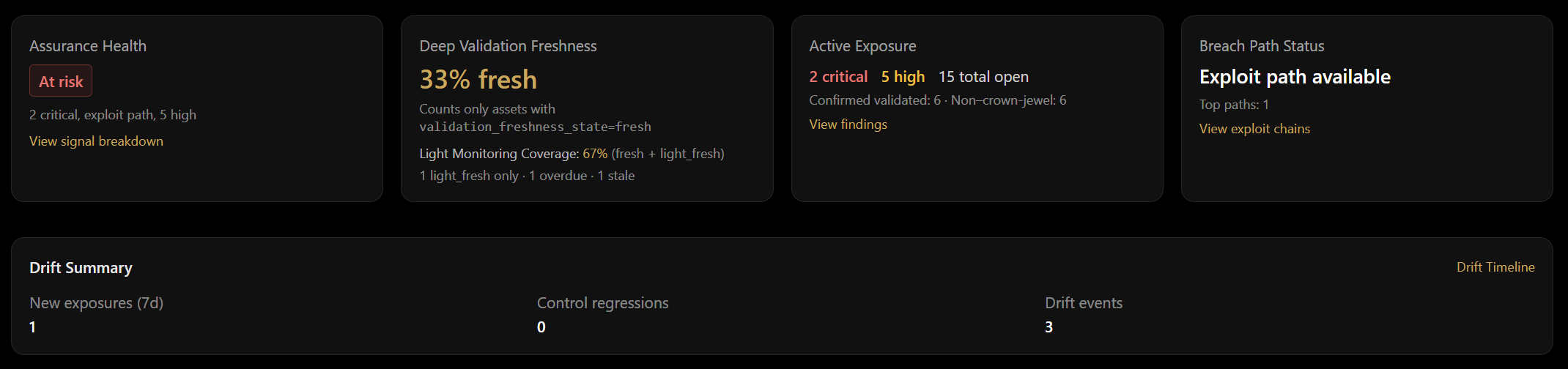
One place to see whether external posture is still holding — or needs attention.
Which external assets were validated, when deeper validation last ran, and what needs attention.
Validated findings stay separate from risk signals, with evidence that supports action.
What changed against the baseline, so teams can reduce exploitable exposure windows.
One place to answer three questions: what is exposed, what changed, and what is verified.
The result is faster review, clearer ownership, and an evidence-backed history of action.
- See whether external posture is holding
- Detect meaningful change across runs
- Track validation freshness by asset
- Focus attention on current exposure
- Maintain evidence of ongoing oversight
Product Detail
Drift, Evidence, and Review-Ready Narratives
Pair the drift timeline with report excerpts so security and compliance can review the same evidence.
Drift reviewed: 3 changes vs baseline
New exposure highlighted: 1 (public endpoint — validated)
Also tracked: 1 dependency change (probable)
1 third-party connection (needs review)
Critical items (period): 0 · High: 1 · Medium / Low: 2
Status: Attention suggested — detail in drift timeline (before / after).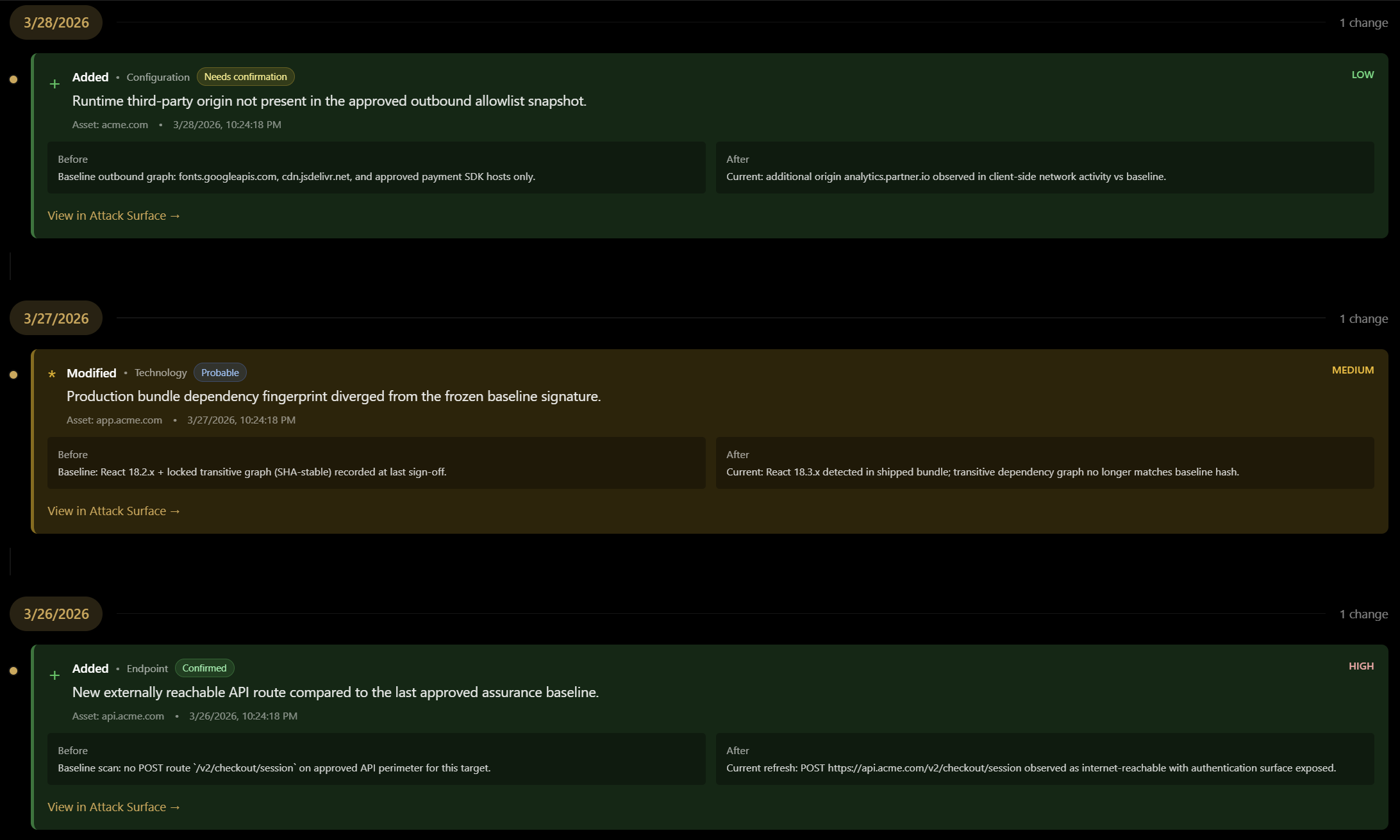
Drift Timeline — What Changed Against the Baseline
04 · Services
What You Can Buy
Core external assurance and optional services built around validation, evidence, and clear review boundaries.
External Attack Surface Assurance
Reduce exploitation risk by validating reachable external risk before promotion and showing what evidence supports action.
Zero-Day & Emerging Threat Monitoring
Maps upstream exploit, release, and advisory signals to observed technologies, sometimes before CVE metadata is complete.
Brand & Domain Impersonation Protection
Track lookalike domains and impersonation signals that can target customers or staff.
AI Shadow Assurance
Track external AI exposure and perimeter-first third-party exposure correlation with clear evidence boundaries.
05 · Process
How It Works
Four steps from scope to verified evidence.
Submit Scope
Provide domains and approved scope under your policy.
Discover & Map
We enumerate internet-facing assets and maintain the surface map.
Verify & Analyze
Reports separate validated findings from risk signals so teams can act without mixing confirmed issues with candidates that need review.
Deliver Evidence
You get reports, drift timeline, validation history, and due-care context for review.
06 · Teams
Use Cases
Different teams, same validation standard.
Enterprise External Assurance
Evidence-backed visibility across complex domain portfolios.
- Multi-domain scope control
- Asset validation freshness
- Drift tracking over time
E-commerce & Public SaaS
Continuous verification for customer-facing surfaces.
- Verified reachability + findings
- Policy‑approved edge posture checks
- Refresh cadence based on plan and scope
Regulated & High-Risk Industries
Evidence package built for regulator and insurer review.
- Latest, selected, and historical due-care views
- Evidence trail per finding
- Policy-enforced guardrails
07 · Review
What Teams Tell Us
Common outcomes: faster review cycles and lower triage noise.
“We finally had one narrative for the board: what was reachable, what was validated, and when we knew it — without a separate spreadsheet war.”
Security Leadership
Enterprise · CISO Office
“Audit prep became easier because findings arrived with evidence packs and timelines attached.”
Risk & Compliance
Financial Services · Security Team
“Daily runs with verified-only escalations cut our triage queue materially — no more treating every scanner line as an emergency.”
Security Operations
Public SaaS · Engineering
08 · Partners
Build With Us
Referral, advisory, MSSP, and technology partners with sales and delivery enablement.
09 · Next Step
See Validation-First Exposure Management in Action
See the workspace, validation flow, and evidence exports in one session.
Book a DemoSee How It Works