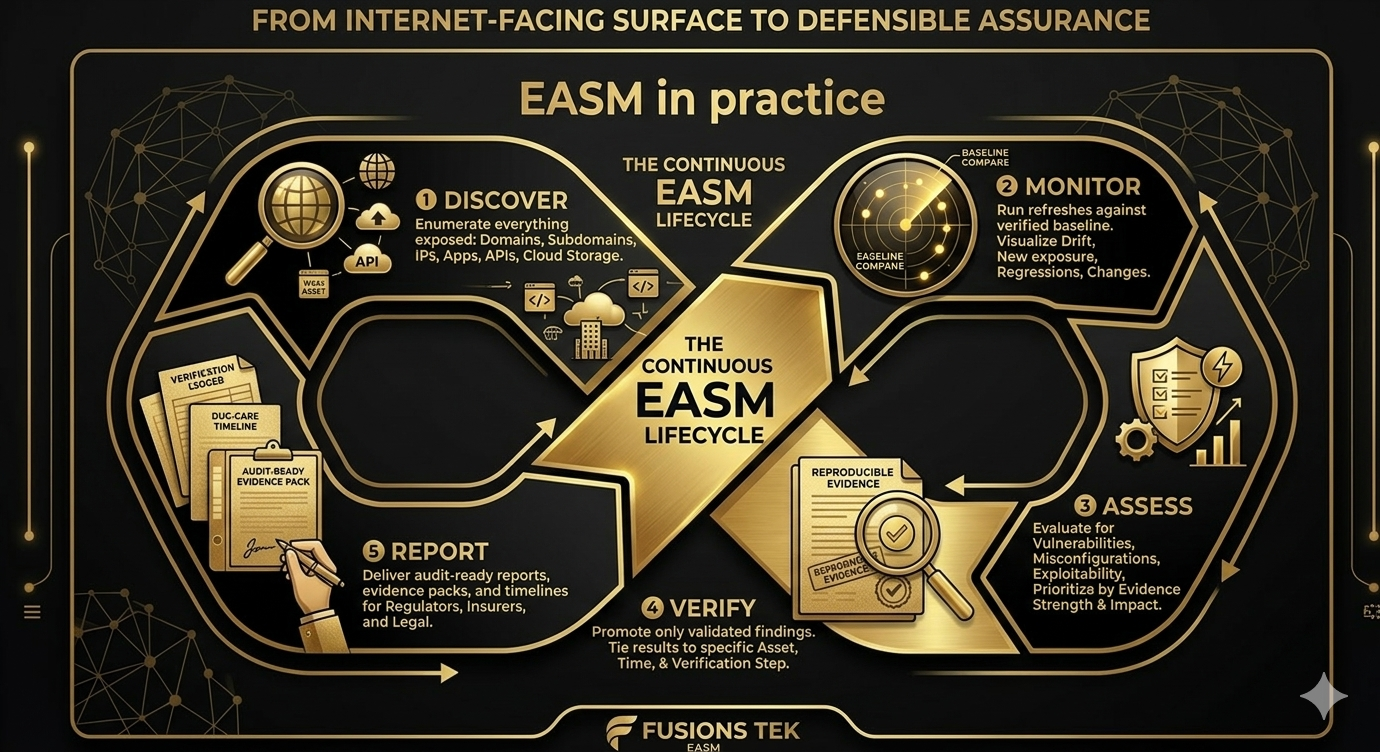
EASM — External Attack Surface Management — is the practice of discovering, monitoring, assessing, and reporting on everything your organisation exposes to the internet. Domains, subdomains, IPs, applications, APIs, cloud resources, and third-party dependencies. The goal is continuous visibility and risk reduction, not a one-off scan. When done right, EASM produces evidence that stands up to regulators, insurers, and post-incident review. That only happens when verification is built in from the start.
This article explains what EASM actually is, how it differs from “scanning a list,” why verification is non-negotiable for assurance, and how a verification ledger and due-care timeline turn EASM into a defensible operating model.
What EASM is — and what it is not
EASM is the discipline of knowing and controlling your external attack surface: everything an attacker can see, enumerate, or reach from the public internet without being inside your network. That includes web applications, APIs, DNS records, TLS endpoints, cloud storage, CDN and WAF configurations, third-party scripts and domains, and any other internet-facing asset that could be targeted or abused.
EASM is not simply “running a vulnerability scanner.” Scanning is one activity within EASM — assessing discovered assets for known issues. But if your idea of EASM is “we have a list of domains and we scan them,” you are missing the core: discovery of what is actually there, continuous monitoring for change (drift), and evidence that what you report is verified and reproducible. Gartner and other analysts have consistently framed EASM as including discovery, inventory, prioritisation, and validation — not just point-in-time scanning (Gartner: Market Guide for External Attack Surface Management).
Discovery vs. scanning
Discovery means finding what is there: enumerating assets that attackers can reach, building a verified map of domains, subdomains, IPs, open ports, URLs, API endpoints, and technology stack. Discovery is ongoing. New subdomains appear. New APIs go live. Cloud buckets are created. DNS and TLS change. If your EASM is only “scan the list we maintain,” you are relying on that list to be complete and up to date. In practice, lists go stale. Real EASM includes continuous discovery — and, critically, comparison of the current surface to a known baseline so that drift (what is new, changed, or gone) is visible.
Scanning is the step that assesses those discovered assets for vulnerabilities, misconfigurations, and exposure. It answers “is this asset weak or misconfigured?” Discovery answers “what assets do we have at all?” You need both. Without discovery, you are only as good as your static list. Without drift detection, you do not know when the surface has changed until an attacker or an auditor tells you.
Why verification matters
Findings without proof do not hold up to auditors, insurers, or post-incident reviews. A report that says “we think you might be exposed” is not the same as “we verified this endpoint at this time and here is the evidence.” Verification means that every finding you report can be reproduced and validated: the test was run, the result was recorded, and the evidence is tied to a specific asset, timestamp, and verification step. That is the difference between a noisy scan dump and an assurance-grade deliverable.
For compliance and risk transfer, the latter is non-negotiable. Regulators and insurers increasingly expect evidence of continuous security oversight — what was tested, when, and what was done about it. A verification ledger is exactly that: a structured record of tests and outcomes. When an auditor asks “how do you know that was fixed?” you point to the ledger: we verified it on this date, with this result. Without verification, you cannot answer that question defensibly.
Verification ledger and due-care timeline
A verification ledger is a structured record of tests and outcomes. Each finding ties back to a specific asset, a specific time, and a specific verification step. It does not only say “we found an issue.” It says “we ran this test, at this time, against this asset, and here is the evidence.” That is what turns EASM output into something you can stand behind in an audit or an insurance review.
Due care means acting as a reasonable organisation would. A due-care timeline shows regular discovery, monitoring, assessment, and remediation — with evidence. It demonstrates that you did not ignore your external surface. Regulators and insurers look for exactly that when assessing whether you met your obligations. NIST guidance on continuous monitoring is clear: security-relevant change has to be monitored and assessed over time, not captured once and treated as static truth (NIST SP 800-137 Information Security Continuous Monitoring). A verification ledger and due-care timeline are the practical implementation of that principle.
Drift: when the surface changes and no one notices
If you run a scan once and never compare the next run to it, you do not know what changed. New exposure can appear — a new API, a forgotten dev subdomain, a misconfigured bucket — and your report still reflects the old snapshot. That gap is silent drift. Attackers re-enumerate on a schedule. When something new appears, they see it. When your tooling does not compare baseline to refresh, you do not. Drift detection is the only way to turn EASM from a point-in-time report into a continuous operating model: establish a verified baseline, run refreshes, and classify the diff — new exposure, regression, removal, or noise — with evidence.
Evidence packs and audit-ready deliverables
Security teams need to know which asset was tested, what was found, whether it was verified, and what should be fixed first. Auditors and insurers need to see that the issue was identified, reviewed, and remediated with defensible external evidence. That is why evidence packs matter: per-finding evidence (what was observed, how it was verified, when) and roll-up deliverables (verification ledger, due-care timeline, executive and technical reports) that support both operations and compliance. The same evidence that helps your team prioritise remediation is the same evidence you can point to when asked “how do you know?”
Policy and guardrails
EASM that runs without policy is a liability. Scope allowlists, consent enforcement, and prohibited-action controls ensure that testing stays within what you have authorised. No brute force, no exploitation unless explicitly approved. The same policies that protect you operationally also support your narrative in an audit: we only tested what was in scope, in the way we said we would. Assurance should be compliance-safe from day one.
What teams should do next
- Treat EASM as discovery plus monitoring plus assessment plus verification. Do not settle for “we scan a list.” Ensure you have continuous discovery and drift detection.
- Insist on verification for every finding you report. Only promote results that can be reproduced and tied to an asset, time, and verification step.
- Maintain a verification ledger and due-care timeline. That is the evidence trail regulators and insurers expect when they ask what was tested and when.
- Run refreshes against a baseline and classify drift. So you know what changed, what mattered, and whether your understanding of the surface is still current.
- Use evidence packs and audit-ready reports. So the same deliverables that guide remediation also support compliance and risk transfer.
Summary
EASM done right is attacker-grade discovery plus evidence-grade visibility. It is not a one-off scan. It is continuous discovery, drift-aware monitoring, verified assessment, and reporting that stands up to regulators and insurers. Verification and audit-ready deliverables — verification ledger, due-care timeline, evidence packs — are what make it defensible over time. That is what EASM is, and why verification matters.